After HIPAA Omnibus, Breach Tally Spikes
Huge Increase in Incidents Under New Notification Guidance
In the year since federal regulators began enforcing the HIPAA Omnibus Rule, there's been a significant spike in the number of major breaches posted on the Department of Health and Human Service's "wall of shame" tally of incidents affecting 500 or more individuals.
See Also: Embracing Digital Risk Protection: Take Your Threat Intelligence to the Next Level
Since HIPAA Omnibus enforcement began last September, the tally has grown by a whopping 67 percent to include 1,126 major incidents, up from 674. The number of individuals affected grew from a total of about 27 million individuals as of late September 2013 to about 38.7 million as of this week, a 43 percent increase (see Wall of Shame: Four Years Later).
Experts say a number of factors contributed to the spike in reported incidents. In addition to the growing mindfulness of HIPAA compliance requirements among many covered entities and business associates - and ramped up regulatory enforcement activities - a significant factor is the HIPAA Omnibus Rule's much more detailed breach notification guidance. In a nutshell, security incidents are now presumed to be reportable unless healthcare organizations demonstrate through the four-factor assessment that risks are low.
Hack Attacks
In addition, an increase in hacking incidents also has contributed to the growth of reported breaches.
"In early 2014, we predicted that there would be an increase in hacking incidents and that the risks of insider threat would increase," says Dan Berger, CEO of security consulting firm Redspin. "So far it appears that we were unfortunately correct. The increased numbers of health records in electronic format make targeting these systems a potentially lucrative endeavor. And we just don't see enough healthcare organizations investing enough in security."
The largest breach added to the wall of shame since HIPAA Omnibus Rule enforcement began is the recent Community Health Systems incident, which affected 4.5 million individuals. The breach, which Community Health Systems first disclosed in a Securities and Exchange Commission filing in August as an incident involving Chinese hackers, is listed on the wall of shame as a "theft," presumably because data was stolen. Some security experts believe hackers gained access to CHS data through a Heartbleed flaw OpenSSL vulnerability.
Another recent hacking incident showing up among the Top 10 largest breaches appearing on the federal tally is an incident at the Montana Department of Public Health and Human Services. In June, Montana state officials confirmed that 1.3 million people were being notified of a breach in which hackers gained access to a public health department server. The breach, however, is listed on OCR's tally as affecting 1.06 million individuals.
Top 10 Breaches
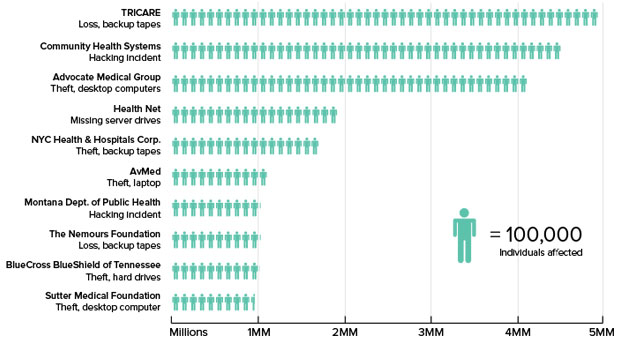
Source: HHS Office for Civil Rights
Awareness Building
Experts are divided on whether HIPAA Omnibus has done enough to spark change and improvement among covered entities and business associates when it comes to their information security practices and compliance efforts.
"The biggest impact that Omnibus has had is in building awareness of HIPAA. Awareness has come a long way," says privacy attorney Scot Ganow of law firm Faruki Ireland & Cox, P.L.L. "HIPAA was seen as toothless tiger, but not anymore. It's finally got teeth."
Under HIPAA Omnibus, business associates became directly liable for HIPAA compliance, and like covered entities, are subject to increased non-compliance penalties that can range up to $1.5 million per HIPAA violation.
Of the 21 HIPAA resolution agreements that OCR has signed, five have occurred since HIPAA Omnibus Rule enforcement went into effect on Sept. 23, 2013, including a record settlement of $4.8 million with New York and Presbyterian Hospital and Columbia University (see $4.8 Million Settlement For Breach). To date no OCR resolution agreements that include monetary settlements have involved business associates.
However, Ganow says that he expects more scrutiny involving BAs to come soon. For instance, OCR's plans to resume its HIPAA audit program, including auditing BAs as well as covered entities, will also have "teeth baring down" for compliance, Ganow says. "The honeymoon is over."
Among the kinds of BAs he thinks will be under the enforcement microscope are cloud vendors. "You can't say you're just a pipe for data," he says of some vendors trying to exempt themselves from compliance obligations and liability.
OCR declined to comment on the latest breach trends reflected in its tally or its enforcement efforts.
Andrew Hicks, director and healthcare practice lead at the risk management consulting firm Coalfire, says that despite the higher potential penalties under HIPAA Omnibus, many business associates - and even some covered entities - still are slow to comply. "We are still seeing organizations that are not fully embracing or acknowledging that they are [liable for] HIPAA compliance," he says. "One year after HIPAA Omnibus ... went into effect, there's still that lack of interest, that lack of desire to become HIPAA compliant."
And Tom Walsh, president and founder of security consulting firm Tom Walsh Consulting, notes: "For smaller business associates, the Omnibus Rule was a cold slap of reality when they discovered there is an entire HIPAA rule dedicated to security that they were supposed to have been in compliance with since last September. Several community based hospitals that I have been working with have been eliminating some of their contracts with smaller business associates. A questionnaire sent out to business associates was quite revealing. Smaller business associates were clueless regarding what security controls they were supposed to have in place. Of course this means that the hospitals' data had been at risk for a long time."
Assessing Incidents
Clearly, however, the HIPAA Omnibus Rule's more extensive guidance on breach notification has played a key role in the surge in the breaches reported in the past year. To determine whether a security incident is a reportable breach, the rule says organizations must take into consideration:
- The nature and extent of the protected health information involved, including types of identifiers, and the likelihood of re-identification;
- The unauthorized party who used the PHI or to whom the disclosure was made;
- Whether PHI was actually acquired or viewed;
- The extent to which the risk to the PHI has been mitigated.
The use of the four factors takes away much of subjectivity that came under the previous so-called "harm standard" for breach notification, which considered the potential financial, reputational, or other harm a security incident might pose to an individual, Redspin's Berger explains.
"Most organizations understand the change in the assessment method," Berger says. "Basically, it takes [into account] certain 'unknowns' and doesn't allow you to use those to conclude that no harm can or will occur."
But compliance attorney Betsy Hodge of the law firm Akerman LLP says some covered entities and business associates have been taking "a more open view of disclosing breaches" by skipping the analysis.
"Some clients have said, 'Our policy is we won't even do the analysis, we will just declare it a breach. We automatically presume that it's a breach, and then we'll provide the needed notification,'" she says.
Berger says the long-term impact of HIPAA Omnibus will depend on how OCR carries out its promises of enforcement activity in the years to come.
"Regulatory changes on their own don't have persistent impact without enforcement," he says. "OCR has recently announced they are getting ready to re-launch their HIPAA audit program and have decided to add on-premises audits back into the mix. I am hoping they make good on their promise to focus more on technical security issues as it is clear that those present the greatest risk of PHI breach."